Protect your business against threats with Business Continuity services
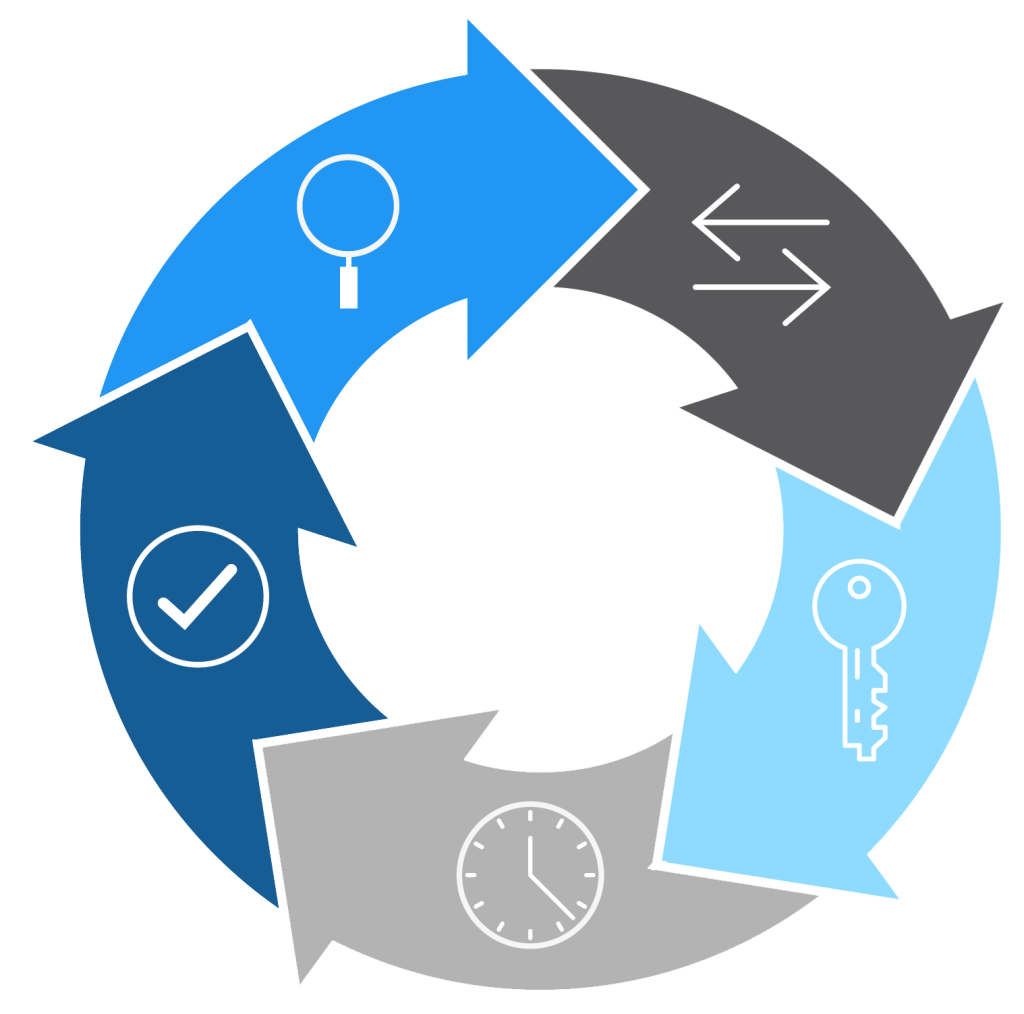
You are prepared for all the different incidents that can harm your business at any time with the Business Continuity plan because it can ensure the uninterrupted operation of your business.
After a thorough review of your processes, we design and execute best practices to ensure business continuity with market-leading solutions and based on your specific needs.
After a thorough review of your processes, we design and execute best practices to ensure business continuity with market-leading solutions and based on your specific needs.