Business Continuity
#imetrixbcp
Business Continuity
#imetrixbcp
22 years
of experience in a single CLICK!
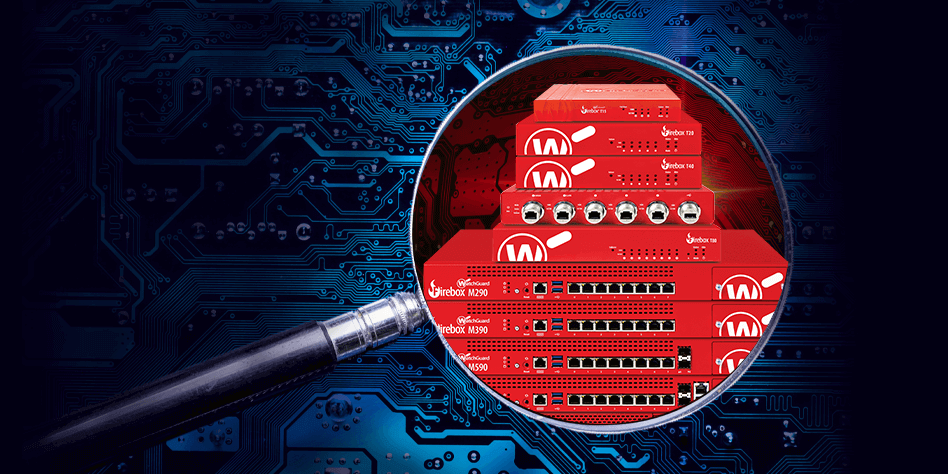
WatchGuard Firebox is a comprehensive advanced network security platform that puts IT security professionals back in charge of their networks with widely deployable, enterprise-grade security and threat visibility tools suitable for any organization, regardless of budget, size, or complexity.
Add other powerful components to strengthen your services even further with advanced protection packs and unique cyber protection capabilities. Control your costs by paying only for the functionalities your clients need.
Enhance your security services with integrated cyber protection that includes full-stack anti-malware. Increase your detection rate and responsiveness to the latest cyberthreats. Extend cyber protection to web browsing, backed-up data, the recovery process, and exploit prevention. Enable investigations by capturing forensic data in backups.


By implementing AI-powered technology and an open, modular range of threat management solutions and services, organizations can spend less time and resources integrating and operating fragmented tools and data sources. The technology can establish efficient, interconnected data exchange, analytics and response processes that transform and enhance security operations capabilities. Vendors can deliver threat management solutions like software, software as a service (SaaS)or as managed services based on client requirements. Solution providers can also custom design, build, manage or provide the tools to deliver all aspects of the threat management lifecycle. Learn More

Includes all features and Products of I-Metrix Business Continuity
The Business Resilience System (BRS), takes delivery of client operations resiliency and end-to-end data protection to a whole new level.




To deliver thorough protection for our partners are based on a multi-stage process rather than simply detecting and blocking threats, leaving other risks uncovered.





T: +30 210.300 2050
Ad: 20-22 Tzortz st. | Athens | GR
24/7 Client Support
22 years of experience in one click! Follow the link to enter to our support suite.
Business Continuity
Operational
Hospitality
Remote Secure
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-advertisement | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Advertisement". |
| cookielawinfo-checkbox-analytics | 1 year | This cookies is set by GDPR Cookie Consent WordPress Plugin. The cookie is used to remember the user consent for the cookies under the category "Analytics". |
| cookielawinfo-checkbox-necessary | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Others". |
| cookielawinfo-checkbox-performance | 1 year | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| elementor | never | This cookie is used by the website's WordPress theme. It allows the website owner to implement or change the website's content in real-time. |
| Cookie | Duration | Description |
|---|---|---|
| pll_language | 1 year | This cookie is set by Polylang plugin for WordPress powered websites. The cookie stores the language code of the last browsed page. |
| Cookie | Duration | Description |
|---|---|---|
| _ga | 2 years | This cookie is installed by Google Analytics. The cookie is used to calculate visitor, session, campaign data and keep track of site usage for the site's analytics report. The cookies store information anonymously and assign a randomly generated number to identify unique visitors. |
| _ga_579L5T1NYX | 2 years | This cookie is installed by Google Analytics. |
| _gat_gtag_UA_203525984_1 | 1 minute | This cookie is set by Google and is used to distinguish users. |
| _gid | 1 day | This cookie is installed by Google Analytics. The cookie is used to store information of how visitors use a website and helps in creating an analytics report of how the website is doing. The data collected including the number visitors, the source where they have come from, and the pages visted in an anonymous form. |
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-functional | 1 year | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| WHMCSy551iLvnhYt7 | session | No description available. |